AT A GLANCE

The integration team plays a crucial role at LENSEC. They do the back-end software development, working with Perspective VMS® to make sure that important features will work. They focus on identifying useful features in third-party physical security software and incorporating data from those features into our video management software.
Integration is necessary to incorporate camera features, access control systems, intrusion detection, video analytics software, third-party software, and IP devices. For example, this team will work with capturing data from other software or firmware using an API or an SDK.
API – Application Programming Interface – An interface allowing LENSEC’s software to interact with other third-party software. This interface helps programmers reconcile data or commands from one software into usable data or commands for secondary software.
SDK – Software Development Kit – This kit includes a library of software, utilities, and instructions for incorporating relevant software features into another software. SDKs are origination sources for software programs. They might also be referred to as a “devkit.”

Waseem Al Sawalha
LENSEC Integration Team Leader
Waseem Al-Sawalha is the Technical Team Lead working on third party software integration for LENSEC. He is a veteran software engineer who manages the development of software APIs and SDKs in Perspective VMS®. Al-Sawalha says, “The team approach is to support the most useful features that a camera model or third-party software offers.”
Al-Sawalha’s team identifies the key features, determining how they can be best-used in Perspective VMS®. Examples here are defined for key camera features that the team might seek to integrate into PVMS.
- Video Stream: The camera streams for H.264 and MJPEG video codecs are the most commonly used within the physical security industry. This is a basic integration.
- Image Snapshot: This feature captures and provides a downloadable snapshot image from any camera views. This is a basic integration.
- Live Audio Streaming: The integration enables PVMS to stream camera audio and capture the recording in sync with the associated camera video. This is a basic integration.
- PTZ Controls: PTZ cameras might use different protocols to move cameras mechanically. Integrating these protocols into PVMS ensures that users can access software controls to pan, tilt, or zoom the camera as needed. This is a basic integration.
- Bi-directional Audio: This feature captures incoming audio and enables the user to trigger a PC-connected microphone and camera-associated speaker to have a two-way conversation.
- Digital I/O: Integration of digital input/outputs on the camera allow event-based triggers. PVMS uses Workflows to define If-This-Then-That routines.
- Edge Motion Detection: Cameras with Edge Motion Detection have on-board algorithms detecting video motion. The data is collected and sent to PVMS. The software integration enables motion detection events to be logged and notifications sent based on motion activity.
- Edge Recording: Cameras with Edge Recording have on-board storage that captures video recordings at the camera. The software integration enables PVMS to import the video from the camera to cover any gaps in connectivity that may result in losing video.
- Edge Analytics: Certain cameras have Edge Analytics on-board. When PVMS integrates these analytics, data can be collected for intrusion detection, license plate recognition, or face recognition. Edge Analytics still require an additional server hosting the database for comparison to the captured images.
- Dynamic Resolution: Some cameras allow integration to dynamically change the streaming resolution. When this is enabled, PVMS can dictate the camera resolution without accessing the camera settings directly.

Jeff Kellick
LENSEC Chief Product Officer
Jeff Kellick, Chief Product Officer for LENSEC, points out All these items are not included for every make or model of camera. Some camera manufacturers might offer these features, and some might not. Beneficial features are selected based on customer requests. Kellick says, “The integration team is taking on more and more features per camera as they are developed. When feature requests come in, we must specifically look at what the customer needs with the camera models they’re putting in place.”
When possible, the integration team prefers to implement new features using the ONVIF standard. ONVIF creates a standard for how IP products designed for video surveillance and physical security purposes can communicate with each other.
Al-Sawalha says, “A lot of manufacturers are adopting the ONVIF standard. When a feature is supported in ONVIF, we can test the feature to validate that it is working using the ONVIF integration in PVMS. In some cases, we might have to make some minor code changes to make sure that the feature will work using ONVIF. If ONVIF doesn’t support the feature, we would need to use a manufacturer-specific integration using the API or SDK.”
The LENSEC integration team also works to integrate physical security software and IP devices in addition to CCTV cameras. Software development for IP device integration involves reading events and alarms and retrieving that information for use in Perspective VMS®. This includes access control devices, RFID readers, anything that generates events that can be leveraged in PVMS.
This is where notifications and workflows come into the picture. The integration team can capture the event info and create a notification that will show in the PVMS action panel or display a visual alert on a map item. Workflows included in Perspective VMS® Professional and Enterprise additions can generate If-This-Then-That scenarios to use triggers and create actions within the software.
Users can also leverage these workflows to integrate physical and logical inputs into on-screen display actions or other notification alerts through associating objects, triggers, and actions.
| TRIGGERS | ACTIONS |
|---|---|
| Custom Action Buttons | Auto-Adjust Archive Configuration |
| Login Notifications | Trigger Camera Outputs |
| Camera Input Triggers | Generate Email Notifications |
| Upon Camera Events | Go to PTZ Presets |
| Upon Alarm or Perimeter Alerts | Create Real-Time Video Extractions |
| Upon System Warnings | Adjust Camera FPS and/or Video Resolutions |
LENSEC is actively working on PVMS integration for many well-known access control systems, fire and intrusion panels, RFID software, and perimeter intrusion detection systems. This work is ongoing and new integrations are being researched and added to our software roadmap as Perspective VMS® continues to develop as a full-fledged, open architecture, enterprise video management software.
If you have specific questions about software integrations for cameras, third party software, or IP devices, please reach out to our sales team or partner services team to learn more.

At LENSEC, we talk a lot about how to unify the security footprint. This includes bringing many different pieces of the security puzzle together, consolidating independent pieces of software and hardware to strengthen the entire physical security deployment.
LENSEC manufactures Perspective VMS® enterprise video management software. We strive to enhance our product by ensuring that it works well with security software and hardware manufactured by other companies in the industry.
The goal of doing this is to make software easier for the end-user to use. If the user can accomplish functions of various security tasks within the video management software, then it avoids the need to jump between software to accomplish basic tasks.
For LENSEC, this requires partnering with security technology companies and integrating software products. An example of this is enabling Perspective VMS® to pull alerts from an access control software, notify key users about activity, and leveraging reports to generate information about those alerts. Additionally, access control software might be able to use video captured by PVMS and play video related to specific alerts in their software.
While this is a general example, LENSEC software developers have identified several useful integration capabilities that end-users or security integrators can employ to strengthen the physical security footprint.
In a recent webinar for new and potential partners, I spoke about several considerations and best practices they might consider when planning a deployment an integrated solution for a unified security project.
Planning the Project
When you’re looking at the integrated security footprint, you must consider how you want to plan the project. This starts with an evaluation. This could be right after you’ve met with the customer and discussed their ideas about what they are wanting to accomplish. You must evaluate the project to see if it is something you can accomplish. Is your team qualified to perform the job?
Part of planning the project is assessing the risk involved. This could be your risk assumed by taking on the job or it could be the risk you identify on behalf of your customer. When you go on-site for a survey of the potential project, you get a good look at their vulnerabilities. They may even be unaware the vulnerabilities exist. But, you may be able to provide insight into risks they have not considered.
You want to help them decide how they should deploy their security system. This could be recommending camera placement, identifying access control reader locations, or even suggesting the addition of lighting in a parking lot to prevent vandalism or theft. If the customer has plans for advanced integration, such as asset management or fleet security management, then you need to consider if you have the right resources to accomplish the project.
When you are helping the customer plan out the project, you may have recommendations that are new to them or that they haven’t considered. Partnering with LENSEC can help you with determining valid solutions for potential projects. LENSEC has over twenty years’ experience in the physical security industry. Some LENSEC history includes time as a systems integrator. We have people still on our team from that time. Some of our former project managers are now solutions engineers or application experts. These professionals can bring ideas into play that are seriously helpful for your customers.
Part of the job of planning the project includes keeping the stakeholders informed. You must be sure that important parties are updated on parts of the project that impact their area of influence. If you don’t know, ask who has a stake in the project early in your planning. It’s never good when an important stakeholder gets involved late in the planning process or after the project deployment has begun.
Potential Project Stakeholders
- Purchasing Department: decides on funding; rates project delivery criteria; and determines contractual agreements
- Campus Security Police: determines hardware placement; oversees security footprint management; and sets criteria for security system expectations
- IT Department: determines network architecture and infrastructure; sets guidelines for incorporating system into the network; and determines network security team
- Compliance Personnel: assess the risk involved and evaluates compliance with privacy laws
- Administration: reports to governing board or organization leadership
Software Integration
When an integrator is putting together the plan for their customer, they must ask specific questions to investigate the needs. Here is where a deep level of understanding the project comes into play. Many times, the customer will know what they want to accomplish, but they probably don’t understand how to get the desired end-result.
The integrator’s job is to put together a puzzle made of security solutions that achieve the desired result. In today’s technical culture, there are many disparate options available. But, the smart integrator will work to unify the security enterprise and design the systems of this security puzzle with interactive features, making the customer’s job easier.
The engineering team at LENSEC understands this need and is working to provide an integration capability in Perspective VMS®. The team is working to develop a world-class video management software that leverages a web application, avoiding a thick client software platform.
Choosing software that already is integrated with security solutions, such as access control systems, assets management systems, or building integration systems, is imperative. It’s important because enterprise-level software meets customer needs. When these disparate software management products can work in unison, life is easier for the end-user.
Hardware Integration
IP Device integration also helps provide solutions that can be beneficial to the security footprint. Engineers at LENSEC have identified hardware that works well with Perspective VMS® for a variety of use-case scenarios. Our team has developed solutions using common off-the-shelf (COTS) hardware, meeting a specific need and application requirement.
Our engineers are prepared to recommend solutions for fleet security management, for example. This leverages onboard, rugged video servers, vehicle-mounted IP cameras, and a variety of additional equipment that interfaces with the vehicle. Our design can deliver video and metadata to central data storage via Wi-Fi connections at the fleet depot. Now the transportation department can bring video and vehicle data under the security footprint for an entire enterprise.
In another example, our engineers devised a solution for the remote solar deployment of surveillance equipment. The stand-alone surveillance solution can operate in areas where there is no infrastructure supporting the equipment. This scenario is useful for oil & gas well sites. These sites require monitoring, though they are in remote locations with very limited infrastructure. Our engineers put together a solution that allows the end-user to log into the NVR remotely, monitor the site, or even receive notifications when activity is detected. This keeps the oil & gas companies from deploying personnel to check sites unless problems are detected. As a result, the company spends less time and money on their monitoring efforts.
Workflows
Our engineers have integrated hardware solutions for drone video, building systems, security gates, video analytics, RFID asset tracking, and much more. In many of these solutions, project engineers are leveraging workflows in PVMS. This is a business logic capability that uses ‘If-This-Then-That’ logic to trigger certain actions in the software based on events or alerts. For example, when a vehicle pulls up to a security gate, a workflow can be created to use data and third-party software to recognize an RFID signal and trigger the gate to open based on the signal received.
Summary
These are just a few examples of many solutions our engineers are designing to meet customer needs. Our team is working hard to develop solutions that work well with Perspective VMS in an enterprise security footprint. If you have questions for our team about solutions, please reach out and let us know.

The system architecture design of Perspective VMS® is flexible to suit the varying demands of each customer. At its core, PVMS is a web server application distributed to clients through a browser-based interface. The network connection from PVMS Services to the client workstation is via a LAN/WAN/GAN.
Network
Perspective VMS® is a network-connected Video Management Software application. To view the PVMS web-client you will need established connectivity with your security network. The security network may be a closed Local Area Network (LAN) or available over the internet on a Wide Area Network (WAN).
Perspective VMS® uses several default TCP connections for accessing services. By default, your network administrator will need to allow the following ports:
4530: For Live Streaming
8090: For Live Proxy Streaming
8091: For Archive Streaming and Extractions
943: If using Cross-Domain Access
443: If using SSL Connections
Servers/Services
PVMS leverages windows-based services for the distribution of jobs performed for managing video. These are typically distributed among system servers. PVMS Services are outlined in detail as follows:
PVMS System Services
Database Server – PVMS Leverages a Microsoft SQL Server Platform (Express/Standard/Enterprise) for transactional data warehousing.
Web Application – The PVMS user interface is presented as a Web Application by Internet Information Services (IIS) from Microsoft.
Administrative Service – The Administrative Service monitors and checks hard drives for the right utilization; checks how much free space on the drive(s); and subsequently purges old archives or moves them to a different offsite location. This service is also responsible for importing and ensuring user synchronization between Active Directory and PVMS.
Health Monitor Service – The Health Monitor Service checks if system cameras defined in PVMS are up and running. If not, the service will notify the user about the offline status of the camera in question. The service also generates health reports related to cameras, servers, and other system components.
Streaming Service – The Streaming Service acts as an intermediary agent between PVMS and system cameras. The service is responsible for handling the video streams and passing them to the system. It is also responsible for streaming archive video that is created using Archiving Service.
Archiving Service – The Archive Service provides for archiving image and video streams from system cameras, handling image extraction requests from users and creating archives and extractions accordingly. This service also manages live recording requests from users to capture camera video streams and encodes them using an H.264/MPEG-4 codec for optimal quality and size.
External System Service – The Integration Communication Service communicates using independent packages from PVMS. The service acts as an intermediary communication agent between PVMS and 3rd party software/hardware applications (RFID, Video Analytics, Access Control, etc.)
Analytics Service – The Analytics Service generates server-based video analytic events and integrations with 3rd party analytics providers.
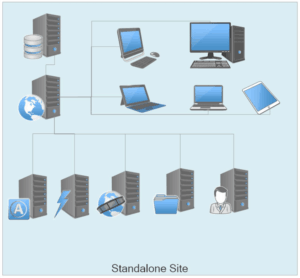
Standalone Site Architecture
In a standalone site, all your services can reside on one computer. This is typically a smaller site with a simple deployment.
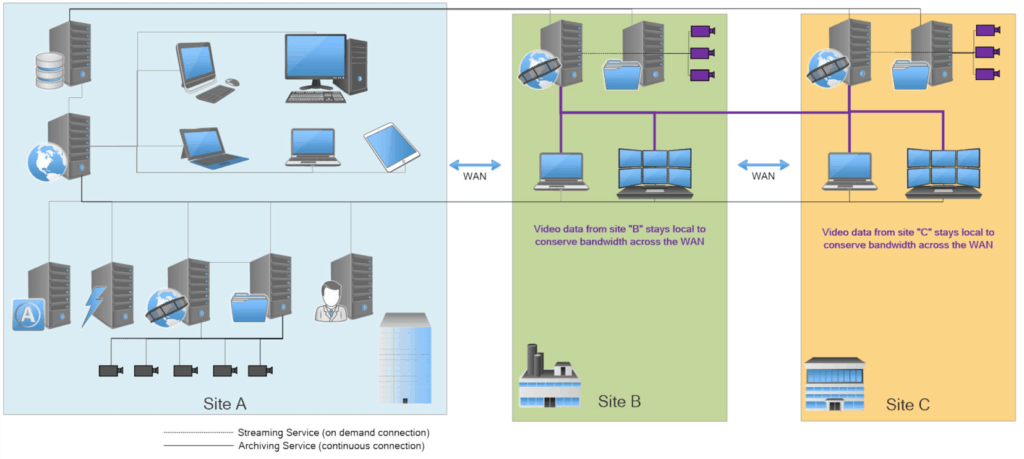
Enterprise Site Architecture
An Enterprise site advances to more complex system architecture. The site might have multiple locations that are connected across the WAN. The subsites don’t need to run all the services. They can run only the streaming and archive services locally and then connect across the WAN to the other services.
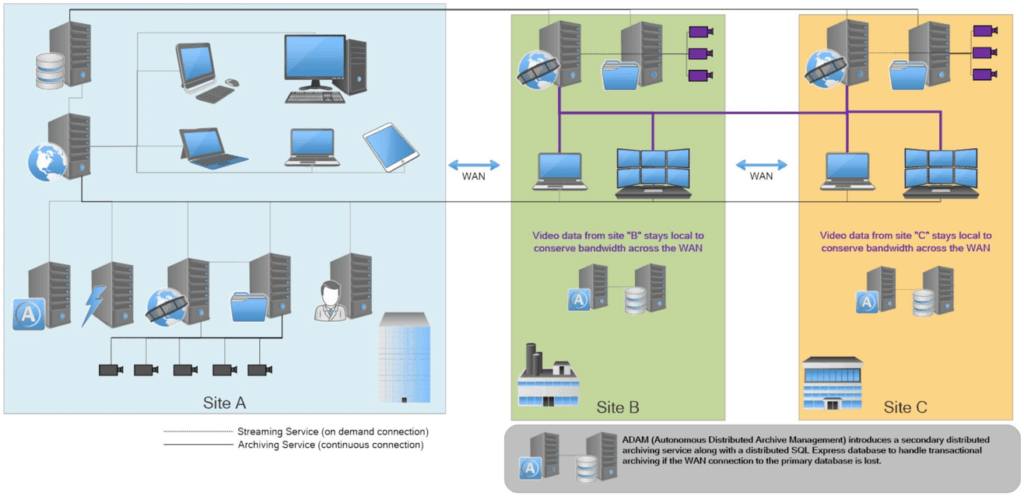
Enterprise System Architecture with ADAM
ADAM stands for Autonomous Distributed Archive Management. ADAM introduces a secondary distributed archiving service along with a distributes SQL Express database to handle transactions archiving if the WAN connection to the primary database is lost. It doesn’t replace the main databases. But, it supplements the database in case the connection goes down. When the connection becomes stable, it automatically transfers the archives and transactions back to the main system.
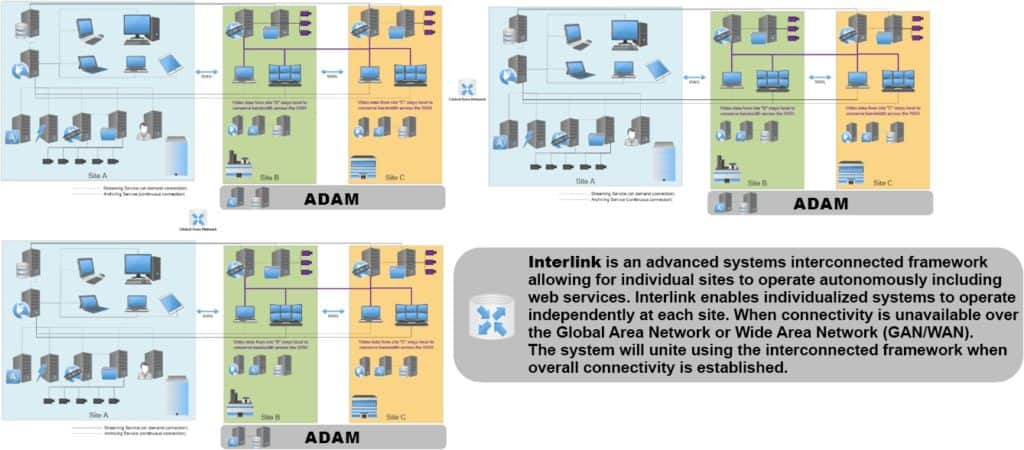
Enterprise System Architecture with Interlink
In Perspective VMS® Version 4.0.0, LENSEC has added Interlink, an interconnected framework for advanced enterprise systems. PVMS Interlink is designed for a distributed multi-site. This is an advanced framework of interconnected systems. These allow for individual sites to operate fully autonomously, including web services. The primary differentiator this functionality introduces is individual web hosts at each site. This can maintain local connectivity when the network connection is lost over the Global Area Network (GAN/WAN) and full functionality of the application must remain. The systems unite under an interconnected framework when overall connectivity is established.
Of course, site architecture varies greatly depending on each site and the variables involved. Our partner services team is available to help partners make wise decisions regarding system architecture. If you need assistance with planning architecture for a deployment, feel free to talk with our partner services team to learn more.

LENSEC is pleased to announce our partnership with Dobil Laboratories. For 48 years, Dobil Laboratories Systems Integration in Pittsburgh, PA has been a trailblazer in Audio & Video. Over that time they have expanded their focus and business to include electronic security. In November of 2018, after a thorough review of LENSEC’s Perspective VMS® offering, Dobil Laboratories joined the LENSEC family and became an authorized reseller.
At Dobil, they know a complete electronic security solution is not one-size-fits-all. The Dobil team will do a security assessment and consult with their customers to customize a solution around their needs, bringing unmatched industry expertise. Security experts will help you identify your vulnerabilities and implement the right mix of security strategies and solutions, such as comprehensive, IP-based access control, rules-based intrusion, and IP-based video surveillance.
Charlie Druzak is the Security Sales Executive at Dobil Laboratories. Druzak says Perspective VMS® is very intuitive to use. He says, “What I love about LENSEC’s video management software is how we can easily interact, not only with the IP-based access control but other security devices right from their interface. The workflows allow you to automate almost any custom output that you are looking for. I have worked in the security industry for over 20 years and Perspective VMS® by LENSEC is by far the best VMS I have seen, and I have sold all of the main VMS products over the years.”
David Rosenberger is the VP of Dobil Laboratories. Rosenberger says they treat their customers as part of the family. Rosenberger says, “We do our best to include them in all our events and our achievements. Customers tend to stay with us so much so that when they leave their firm and move to another, they bring us with them. It’s simple, our job is to make them look good and if we achieve that then they will keep coming back. That is why partnering with LENSEC was an easy decision for Dobil because we knew that PVMS makes the customer look good and be able to do their jobs more efficiently and effectively.”

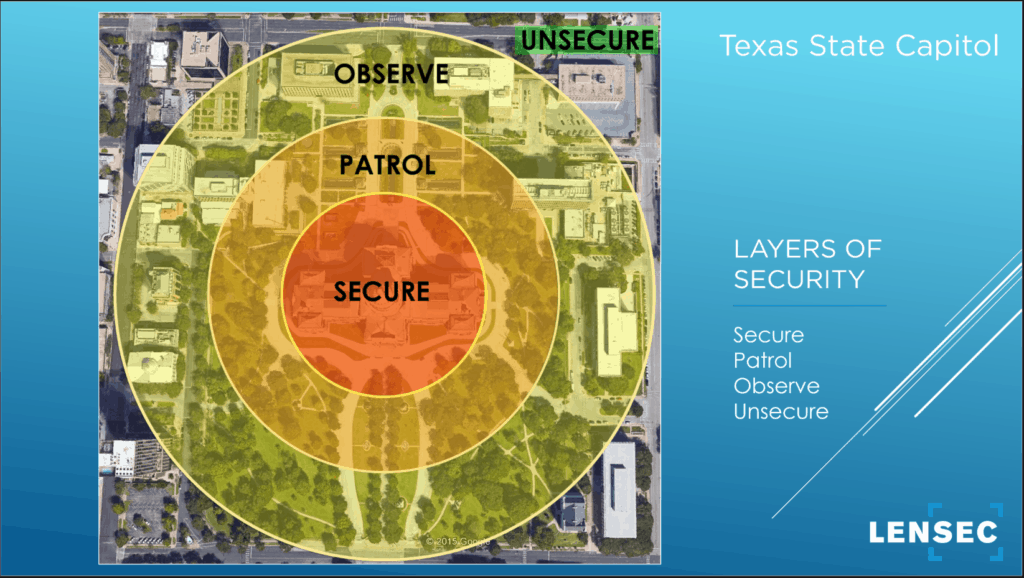
When you are evaluating a site and its surroundings for purposes of a security project deployment, it’s important to consider the layers of security around the location. The needs at a specific site can and will vary greatly depending on the project requirements. The idea of “layers of security” is simple and can be applied with adaptation to each physical security project. Consider this image that I’ve applied to the State Capitol in Austin, TX.
This is a big property with many high-level assets. Many important people are making their way in and out of this building every day. The Capitol Police force is charged with maintaining security on this property covering a large area.
Secure
When we look at the capitol building itself, we see a central location where all major assets and personnel converge. The center area is considered as the highest target for security. This is the Secure Zone. For the security plan, you will need the highest number of CCTV cameras in this zone.
Patrol
In the next ring out, we have the Patrol Zone. This is still on the property but it’s a less secure area. This specific location has a park-like setting surrounding the capitol building. This is an environmentally designed area that separates the secure area from busy, crowded streets downtown. The pathways and driveways are controlled and through-traffic is restricted. It’s a space that is designed to be used and enjoyed by the public, but it doubles as a security layer surrounding the Secure Zone. We call this a patrol area because the Capitol Police force protects this area. They might do this by foot patrol, limited vehicle patrol, or surveillance monitoring. But, it’s important to note, they don’t have as many cameras, security devices, or personnel in the Patrol Zone as they would in the Secure Zone. We’re moving away from a high priority area to a medium priority area.
Observe
As we move further away from the State Capitol building, we enter the Observe Zone. This is an area that surrounds the park and includes some city streets and surrounding buildings. The Observe Zone will be low-priority in comparison to the Patrol Zone and Secure Zone. There will be fewer cameras covering this area. Foot patrols will decrease. And, the area may even limit the number of vehicle patrols. Enforcement and monitoring measures are decreasing as we move further away from the central target of security. The Capitol police are going to keep an eye on these areas for potential threats, but they are minimizing the amount of attention needed for outlying areas.
Unsecured
Finally, there is an unsecured zone on the outer edge. This area may not be monitored at all with CCTV cameras or patrols. Citizens can move through this area unrestricted and not monitored.
The security manager can take these concentric rings of security and apply it to any site. It can be modified to fit certain scenarios and adapted for many different sites requiring security.

LENSEC has released the latest version Perspective VMS®. PVMS v4.0.0 is a major release with new features and enhancements. Some of the highlighted features are available below:
| PVMS® v4.0 Features | Description |
|---|---|
| Analytic Rules Administration | Ability within the integrations section of administration for naming and associating analytic rules with cameras for use in alerts and workflows |
| Android Mobile App Connection | Connection with version 4.x to Android mobile application |
| Antenna (RFID) Administration | Ability within the integrations section of administration for naming and associating RFID antennas with cameras for use in alerts and workflows |
| Connectors Administration | Ability within the integrations section of administration for naming and associating connectors (3rd-party controlling or reference objects) with devices for use in alerts and workflows |
| Custom Map Shapes | Ability to design custom shapes for placement on a map |
| Custom Reports | Ability to save custom report filters and configurations |
| Event-based Trigger (Multiple Cameras) | Ability to initiate/trigger a programmable action (via workflow routine) based a defined an event from multiple cameras selected at once |
| Event-based Trigger (White list / Black list) | Ability to initiate/trigger a programmable action (via workflow routine) based an defined an event from a configured control list |
| Filterable Fleet Timeline Events Legend | Ability to filter via select box on timeline legend events for population in corresponding timeline |
| Fleet Security Management Module | Ability to manage multiple fleet vehicles/devices centrally for viewing video across a timeline of events and including the ability for vehicle incident export |
| H.265 Support - Archiving | Ability to archive video in H.265 (HEVC) format |
| Highlight Tags | Ability to mark/highlight an area of interest within a tagged event |
| Interlink Remote Connection | Ability to link multiple remote independent sites for integrated client management |
| Pelco Analog PTZ (Pelco D) Support | Ability to support integration with analog Pelco-D PTZ control signals |
| User Defined Side Panel Position Preference | Ability to maintain preferred state of side panel (minimized/maximized) across user sessions |
| Vehicle Incident Events | Ability to store vehicle video incidents for retrieval end extraction |
| Virtual Vehicle Speedometer | Ability to track of vehicle’s speed during transit route in association with video |
| Scheduled Access Login Limitation | Ability to restrict users access to the VMS during selected schedules |
| Fast Archive Rewind | Enhancement: Allows for immediate rewind of MJPEG archiving from live view regardless of position in time of video/archive file generation. |
| Administration Service | Enhancement: Improved handling of faulty disks during file management routines |
| Events Panel – Archive Playback | Enhancement: Allows ability to play audio in events info panel playback |
| Active Directory Integration | Enhancement: Supports removal of users no longer listed in Active Directory |
| Camera List (Administration) | Enhancement: Added column for Monitored camera attribute |
| Extractions Permissions | Enhancement: Added ability to share extractions to a group (similar to presets and sequences) |
| SDK/API | Enhancement: Various enhancements to Module control via API for 3rd-Party integrations |
| Archive Timeline Control | Enhancement: Allow for ability to drill into active timeline slider for quick navigation |
| Connectors | Enhancement: Renamed integration connectors for better interpretation of object |
| Web Service | Enhancement: Ability for Perspective VMS to operate as a client on Linux Unbuntu |
The full release notes for PVMS Version 4.0.0 are available on the LENSEC website downloads page and the Perspective VMS® product page. In addition, the downloads page is where you can find the latest software download for PVMS v4.0.0.
If you need assistance, please don’t hesitate to contact our support team. Thanks for trusting in LENSEC and Perspective VMS®.
Upcoming LENSEC Events
LENSEC PVMS Technical & Sales Training Dates
Houston, TX, USA
TECHNICAL CERTIFICATION TRAINING
DATE: August 15-16, 2019
LOCATION: LENSEC Headquarters
Houston, TX
GSX (ASIS) SALES TRAINING
DATE: September 9, 2019
LOCATION: Hilton Garden Inn
Chicago McCormick Place
Chicago, IL
TECHNICAL CERTIFICATION TRAINING
DATE: October 17-18, 2019
LOCATION: LENSEC Headquarters
Houston, TX
ADDITIONAL TRAINING DATES
IN HOUSTON & REGIONAL LOCATIONS
THROUGHOUT THE YEAR
ASIS SecurityXchange 2019
Park City, UT, USA
DATE: August 11-14, 2019
LOCATION: The Lodges at Deer Valley | Park City, UT

Global Security Exchange (ASIS) 2019
Chicago, IL
DATE: September 9-12, 2019
LOCATION: Hilton Garden Inn
Chicago McCormick Place
123 E Cermak Road
Suite #300, Room #TBD
Chicago, IL 60616

LENSEC Headquarters
3151 Briarpark Drive, Suite 125
Houston, TX 77042 United States
LENSEC.com | +1 (713) 395-0800
Contact Us for a PVMS
Sales Demonstration or
Free 30-Day Software Trial