AT A GLANCE
PRODUCT: PVMS Offers New Software Integration With Galaxy Control Systems
SUPPORT: Using PVMS Workflows Management
PARTNER: REPWORKS Manufacturing Reps Added as LENSEC Partner
PVMS SOLUTION: Using Solar as a Power Source
NETWORK SECURITY: LENSEC Expert Helps With Network Security Vulnerabilities
CASE STUDY: AACPS Schools Use PVMS to Keep Students Safe
The LENSEC Perspective Newsletter – January 2018
PRODUCT: Perspective VMS® Offers New Software Integration with Galaxy Control System’s Cloud Concierge
Bi-Directional Integration Delivers Access Control and Video Surveillance Across Security Systems


LENSEC is pleased to be partnering with Galaxy Control Systems to provide full-featured integration between Perspective VMS® and System Galaxy software and Cloud Concierge®.
Cloud Concierge® provides full-featured, cloud-based access control services. When paired with LENSEC’s Perspective VMS®, the unified security platform gives customers the opportunity to leverage powerful functionality across the entire enterprise. Either Cloud Concierge® or Perspective VMS® can be used as the primary software to monitor security system assets. Users can keep an eye on employee use of access cards throughout the facility and access security video in real-time. True power is achieved when the systems work in unison to notify personnel about crucial events, calling up video as the event occurs. This provides opportunities to act upon notifications to sound alarms or lock/unlock doors.
Authorized personnel are able to access live and archived video, facility maps showing camera locations and views, while monitoring event activity from user dashboards. Event alarms from Cloud Concierge® will display as notifications in Perspective VMS®.
Since 1998, LENSEC has been a trusted security manufacturer collaborating with technology partners, such as Galaxy Control Systems, to provide a powerful unified security platform. We listen closely to our end-users and security integrators to follow the best practices and improve Perspective VMS® based on useful feedback.
LENSEC’s enterprise-level video management software, Perspective VMS® provides real power alongside integrated security solutions. PVMS streams and captures IP security camera video and incorporates video analytics, access control,
and more into the software.
System Galaxy is a complete, enterprise-class access control and security management solution that offers unsurpassed ability to satisfy the requirements of any credential management, access control or security situation. with a user interface that’s easy to operate and system features that deploy in any combination, Galaxy easily fits any customer.
To contact Galaxy Control Systems call 800.445.5560 or email [email protected].
To contact LENSEC call 713.395.0800 or email [email protected].
LENSEC Tech Support Solution
Using PVMS Workflows Management
LENSEC Partner Focus
REPWORKS Manufacturing Reps
Perspective VMS® Solution
Using Solar as a Power Source



Workflows management is a great tool in Perspective VMS® that allows administrators to set up specific actions based on if/then rules when certain events occur within the security environment. With Workflows, administrators configure and manage a logical association of objects, triggers, conditions, and actions that allow for integration of physical and logical inputs into on-screen display actions or other notification alerts.
For example, a rule can be created to cause PVMS to generate an email to a technician or administrator when system storage is reaching capacity. This is just one example of many uses for Perspective VMS® Workflows. Here are a few we use within PVMS to enhance features and functions for administrators.
The Custom Action Button is a user-defined button that can be utilized as a trigger for workflow-based actions. The button may be customized by the configuration user in both text and graphic icon. It will appear where assigned by group permissions on the Actions menu of the Side Panel.
Event-based Triggers provide the ability to initiate or trigger a programmable action via a workflow routine. The trigger is based on a defined event from a configured external input device or from a PVMS system alert.
Virtual Output Actions give administrators the ability to create a daisy chain of multiple output actions based on one event. For example, when a server room door is forced open, an alert is generated causing a camera recording to be created, an email to the system admin is generated with an image snapshot attached, and a user audit log report is generated showing users logged into the system at the time of the incident.
An Automated Real-time Extraction can automatically initiate recording for a pre-defined length of time based upon a triggered event. For example, a gate opens and triggers a 60 second recording from an associated camera.
These are just a few ideas. The possibilities of ways to use workflows are endless. Our customer support team is a good resource for helping technicians and administrators with solutions using PVMS workflows. If need to implement workflows using Perspective VMS®, our customer support team is available to answer questions and provide best practices for your project.
If LENSEC Partner integrator technicians need support, call (713) 395-0800 + Option 1 or email [email protected] for assistance.
LENSEC is proud to announce a new partnership with REPWORKS. This Manufacturing Rep Firm represents LENSEC and Perspective VMS® in the Northeastern United States.
Founded in 1987 by Ted Curtin, CPP, CPMR, REPWORKS has been providing representation for select manufacturers throughout Upstate New York & the six New England states. Curtin is a Certified Protection Professional (CPP) and a Certified Professional Manufacturers Rep (CPMR). He has a long reputation of service within the low voltage integration industry. Curtin is a member of several regional and national industry associations. He also conducts monthly training classes for large audiences of security dealers and consultants on the design and installation of CCTV, security, IP, and AV systems.
REPWORKS offers comprehensive sales/marketing services including technical and promotional service and uncompromising responsiveness. The manufacturing rep firm also handles some of our technology partner companies. Galaxy Control Systems and Razberri Technologies are also professionally represented by REPWORKS. Michael Brimmer, LENSEC’s Director of Sales, North America, says “The partnerships between REPWORKS, as our manufacturer rep, and LENSEC’s technology partners provide good synergy in selling a complete solution. This in turn provides great value for our VAR Partners.”
If you are interested in partnering with LENSEC as an integrator, security consultant, or technology partner, please get in touch with us by email or phone. We’d love to talk with you.
If you’d like to contact REPWORKS, here is there contact info.
REPWORKS Manufacturing Representatives
Phone: (720) 446-3035
Website: http://www.repworks.com/
Email: [email protected]
Find out more about LENSEC’s manufacturing reps and our partnerships on LENSEC’s VAR Partners page. You can also learn who to call in your region to find out more about partnering with the LENSEC team on the Where to Buy PVMS page. If you’d like a sales representative to contact you, please reach out to us by phone or email.
Contact: LENSEC Sales
EMAIL: [email protected]
PHONE: (713) 395-0800
Due to lack of electricity at a security deployment site, a solar solution may be optimal in some locations. In the US, everyone is experiencing extreme freezing weather. Extreme cold, high winds, heavy rain, or even extreme heat, certain areas of the country can prove challenging to maintaining power for video cameras and field security equipment. Loss of power means loss of camera surveillance and archiving – which can be a critical loss for customers using security equipment. Due to lack of electricity at a security deployment site, a solar solution may be optimal in some locations.
LENSEC physical security experts have recently used an equipment solution to receive power from a solar panel and battery backup. The use of solar power as an alternative source of power, in some cases, may be more dependable than battery or electricity for surveillance cameras. Especially for some end-users who require continuous video monitoring where cameras are in remote areas experiencing extreme weather.
Besides environmental, there are other conditions where using solar as a source of power just makes sense:
- Remote sites – locations that do not provide standard IT infrastructure
- Lack of Infrastructure – sites are typically remote and unmanned
- Limited Equipment Space – equipment for a required solution must also fit into a limited amount of physical space
For instance, LENSEC field technicians recently used the solar power solution at a city park – where electricity is not available. Solar power has also been used at a playground for night-time monitoring due to limited electricity during night-time hours at this location. Using solar has also been a great option for cameras mounted on poles when constant power is not available. Technicians prefer this option since it has reduced their need to access cameras mounted high on top of poles.
If you’re interested in learning more about LENSEC’s Solar Solution with Perspective VMS®, the Perspective VMS Solar Solutions Datasheet is available on our website. Call us at (713) 395-0800 or email [email protected] for a software demonstration.
NETWORKING SECURITY: LENSEC Provides Valuable Networking Security Info Regarding Spectre and Meltdown Vulnerabilities
In early January the Meltdown (CVE-2017-5754) and Spectre (CVE-2017-5753, CVE-2017-5715) vulnerabilities were disclosed to the public. Both vulnerabilities could allow an exploit to leak sensitive data due to a CPU feature known as Speculative Execution.
To help optimize speed, a CPU will use its idle time to run computations for data that it believes will be called next. Modern CPUs have done an excellent job of predicting what will be called next, but sometimes this prediction is wrong. When this happens, the CPU discards the data and continues with the correct operation. However, the data remains in the CPU’s cache just in case the CPU needs to retrieve the data in the future. The data that remains can be sensitive in nature such as encryption keys or passwords.
LENSEC’s Senior Systems Support Engineer, Nick Stigers, says the exploits using the Meltdown vulnerability scan the CPU’s cache to reveal the data that’s been left behind. The Meltdown vulnerability affects Intel and some ARM powered machines, while AMD-equipped computers remain mostly unaffected. Stigers explains, “Meltdown exploits are easy to create by hackers, but they are also easy to mitigate via operating system and BIOS updates. “
Spectre exploits, on the other hand, are much tougher to create, but also more difficult to mitigate. Spectre works differently than Meltdown. Rather than finding ways to access the CPU’s cache directly, Stigers says Spectre targets applications installed on the device. According to Stigers, “In a nutshell, Spectre exploits trick applications into running unnecessary speculative actions and leak the data to the exploit. Spectre mitigation is more difficult since it targets any application and essentially all processors from AMD, ARM, and Intel are vulnerable.”
Exploits utilizing both vulnerabilities are designed to leak data and are not designed execute remote code such as installing malware or ransomware. It is also important to note that there are currently no known exploits that have been created to utilize either vulnerabilities, however, applying mitigation should be a top priority.
“Meltdown exploits are easy to create by hackers, but they are also
easy to mitigate via operating system and BIOS updates.”
Nick Stigers, LENSEC Senior Systems Support Engineer
A three-step approach is needed fully protect a device:
Operating System
Operating system updates greatly mitigate the Meltdown vulnerability. Microsoft has released security updates for Windows Server 2012 R2, Windows Server 2008 R2, Windows 10, Windows 8.1, Windows 7 operating systems. These updates are available via Window’s Update.
- Due to incompatibility issues with certain third party antivirus software, Microsoft requires a special registry key be present in order to receive the update via Windows Update. If the device is equipped with a compatible third-party antivirus or Microsoft product (i.e. Windows Defender), then this registry key should already exist. If the key is not present, then contact the antivirus manufacturer. If the device is not running antivirus, then the registry key will need to be set manually.
- Microsoft offers a handy guide for ensuring that the system has been updated and verifying that the protections have been enabled.
Hardware
A BIOS update is necessary to help mitigate Spectre vulnerabilities. HP and Dell initially released BIOS updates for their devices. They have both suspended them as of January 22nd at the recommendation of Intel. Both state that an updated BIOS for their devices will be available soon. For other manufactures, please contact the OEM BIOS manufacturer.
Web Browsers
The most probable access point for Spectre exploits would be through the web browser via malicious java script code. This code can be embedded in a web page or as part of a third-party ad on a page. Mozilla Firefox has implemented fixes in their latest version. Google is advising users to take advantage of security enhancements that are part of the Chrome browser. Security patches for Microsoft Edge and Internet Explorer have been released via Windows Updates.
If you are a LENSEC VAR partner or end-user customer and you want to learn more about how this affects your equipment in your physical security environment, please contact our tech support team for assistance.
CONTACT: LENSEC Technical Support
PHONE: (713) 395-0800 Option 1
EMAIL: [email protected]
CASE STUDY: Anne Arundel County Public School Use Perspective VMS® to Keep Students and Faculty Safe
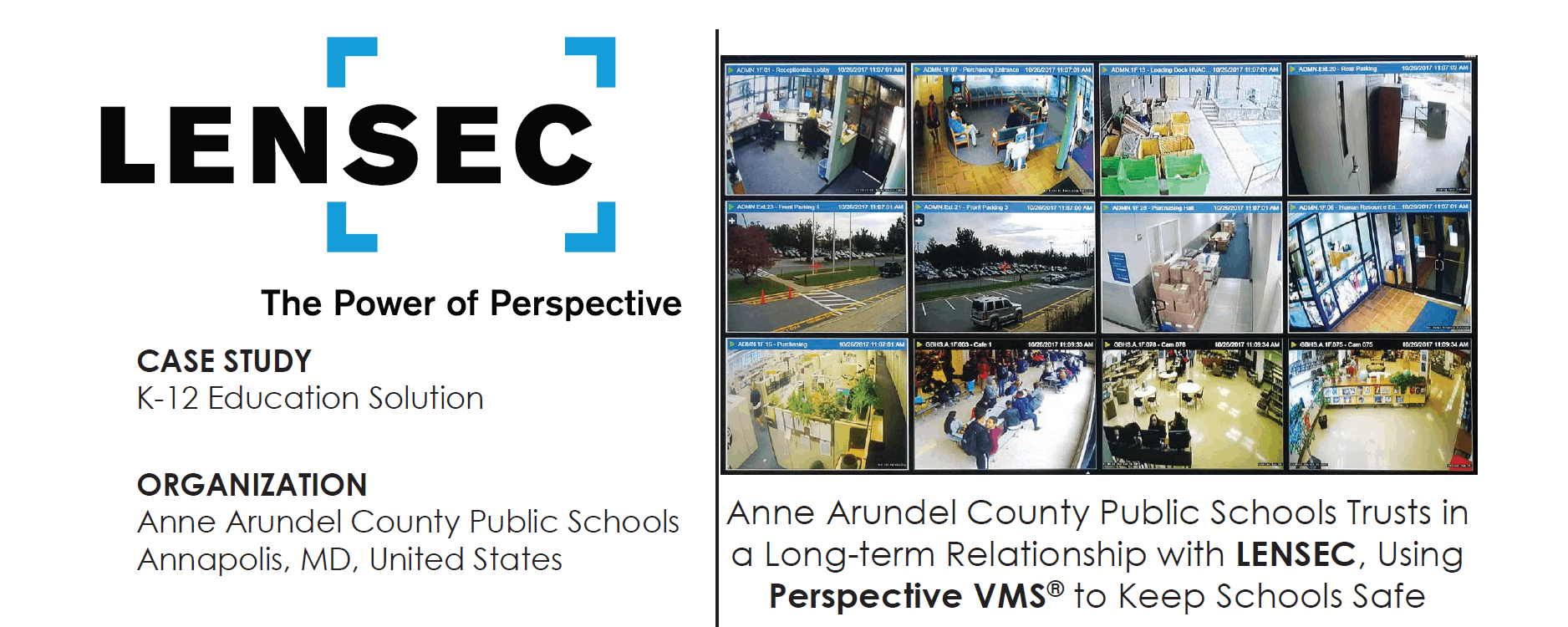
SCENARIO: District-wide IP Video Surveillance
Anne Arundel County Public Schools (AACPS) in Maryland is one of the 50 largest school systems in the United States with over 81,000 students in 126 schools.
THE PROBLEMS: Widespread Coverage Over a Large Region
Having this many students across a sizable school district creates many issues with providing a safe learning environment. A large school district like AACPS is presented with many problems since they have students at campuses spread across a wide regional area. There are many incidents that are investigated at each school. Capturing video evidence can often mean the difference in determining the true facts of each incident.
With each facility, system maintenance and training of users becomes crucial. Care for the components of the security system and the network backbone require ongoing support. Large school districts need vendors they can trust to support their systems and provide needed maintenance on security systems.
SOLUTIONS: Overview
In 2007, AACPS contracted with LENSEC to provide a video surveillance system that could capably cover district properties. Since that time, AACPS has been a loyal customer. LENSEC helped bring the school district onto one security platform. At the time, the district used LENSEC’s legacy video management software, LENSEC VMS. Since then, the district has upgraded LENSEC’s enterprise-level security platform, Perspective VMS®. AACPS began shifting to PVMS in the 2014-2015 school year. The conversion to the new security software was completed in 2017. Perspective VMS® brings many advancements to the district that were not available in LENSEC VMS.
“Our experience has been great. The support has been remarkable. LENSEC is a phone call away and always helpful in getting what I need.”
Doyle Batten
Supervisor of School Security, AACPS
CONCLUSION: PVMS is the Best Solution for 8,000 Cameras
As a large customer, AACPS requires a quick response from LENSEC support staff when help is required. Batten tells us, “Our experience has been great. The support has been remarkable. LENSEC is a phone call away and always helpful in getting what I need.”
With a team in place that knows the needs, LENSEC continues to grow with Anne Arundel County Public Schools. As the district plans to surpass 8,000 cameras in the near future, the school security team can continue to rely on LENSEC and Perspective VMS® for now and into the future.
If you’re interested in learning more about the Perspective VMS® solution for educational districts and campuses, check out the full case study on LENSEC’s K-12 Education Solutions page on our website. Or, you may call us at (713) 395-0800 or email [email protected] for a software demonstration.
LENSEC Headquarters
3151 Briarpark Drive, Suite 125
Houston, TX 77042
LENSEC.com | (713) 395-0800
Contact Us for a PVMS
Sales Demonstration or
Free 30-Day Software Trial